Key Takeaways:
- Zetachain paused cross-chain transactions on Tuesday after an exploit targeting the GatewayZEVM contract’s call function hit internal team wallets.
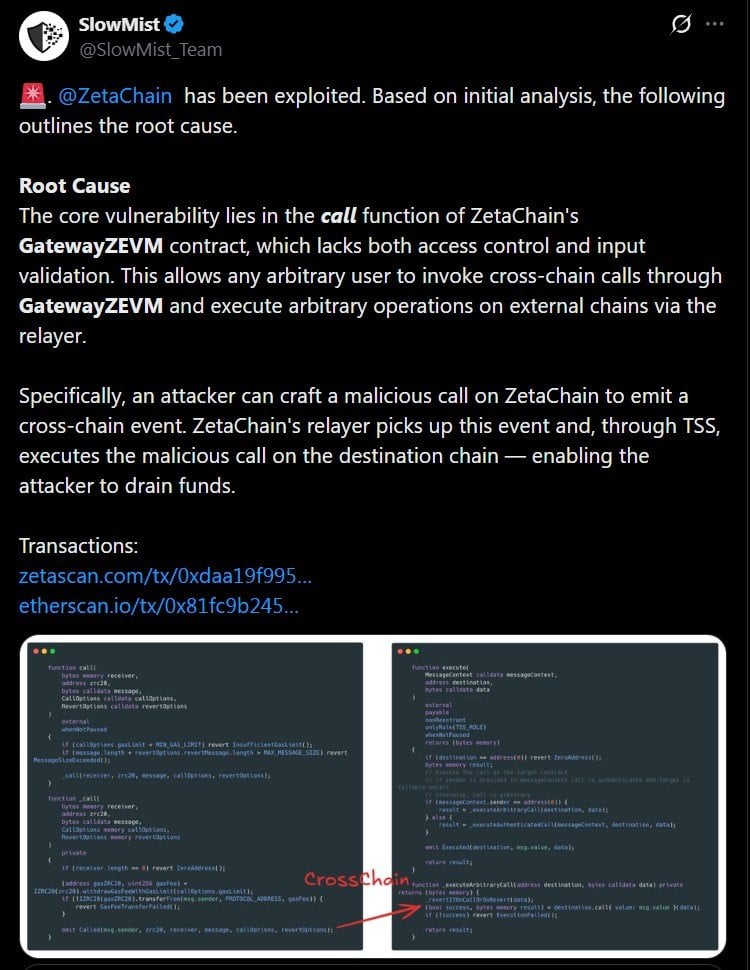
- Slowmist identified the root cause as a missing access control and input validation in the call function, allowing any user to trigger malicious cross-chain calls without authorization.
- The incident marks the second major cross-chain exploit in April 2026, following the KelpDAO hack that triggered the worst DeFi liquidity crunch since 2024.
Slowmist’s Preliminary Analysis
The team pinpointed the GatewayZEVM contract’s call function as being the entry point. The function contained no access control and no input validation, a combination that allowed any external address, without authorization, to trigger malicious cross-chain calls and route them toward arbitrary targets. Wu Blockchain independently confirmed the root cause shortly after.
Zetachain said the exploit affected its own internal team wallets (estimated to be worth $300k), adding that user funds were not directly impacted. The protocol paused cross-chain transactions while its security team assessed the full scope of the breach. A post-mortem is expected once the investigation concludes.
Moreover, the incident arrives at a difficult moment for cross-chain infrastructure as earlier this month, the KelpDAO exploit triggered a cascade of liquidity withdrawals across decentralized finance ( DeFi) protocols, resulting in the worst crunch in DeFi since 2024. The Arbitrum Security Council, however, took emergency action to freeze 30,766 ETH linked to the KelpDAO exploiter.
Access Control Was the Root Issue
Slowmist’s findings have once again highlighted a recurring pattern in smart contract exploits where missing or insufficient access controls are applied on functions that handle sensitive operations. In Zetachain’s case, the call function in GatewayZEVM was deployable by any external address with no permission check, leaving the door open for arbitrary inputs to be processed as legitimate cross-chain instructions.
The absence of an input-validation breakstop compounded the risk because, without checks on what data the function receives, attackers can craft a malicious payload and direct it to unintended destinations across chains (bypassing any assumed trust boundaries within the contract logic).
Security researchers have consistently flagged insufficient access controls as one of the most common and preventable vulnerabilities in production smart contracts. Whether Zetachain’s GatewayZEVM contract had undergone a formal third-party security audit prior to deployment has not been confirmed.